Table of contents
In today’s digital landscape, maintaining the security of your Windows infrastructure is paramount. One of the critical aspects of this security is managing local administrator passwords, which, if mishandled, can become a significant vulnerability.
Say hello to XOAP Windows LAPS DSC a robust solution designed to enhance your security posture by automating the management of local administrator passwords across your Windows environment. ⬇️
What is XOAP Windows LAPS DSC?
XOAP Windows LAPS DSC is a powerful Desired State Configuration (DSC) module that leverages the capabilities of the Local Administrator Password Solution (LAPS) to manage and securely store local administrator passwords on domain-joined machines. By integrating with the DSC framework, XOAP Windows LAPS DSC allows for the automated deployment and configuration of LAPS policies, ensuring that local administrator passwords are unique, randomly generated and periodically updated.
Key features
1. Automated password management: XOAP Windows LAPS DSC automates the generation, storage, and updating of local administrator passwords, significantly reducing the risk of password-related breaches.
2. Centralized control: Manage and monitor password policies centrally using DSC, ensuring consistent security practices across your organization.
3. Seamless integration: Easily integrate with existing Active Directory infrastructures, making deployment straightforward and hassle-free.
4. Compliance and auditing: Meet compliance requirements with detailed auditing capabilities, ensuring password policies are enforced and tracked.
Why use XOAP Windows LAPS DSC?
Enhanced security
Local administrator accounts are often targeted by attackers looking to gain privileged access. By using XOAP Windows LAPS DSC, you make sure that each local administrator password is unique and regularly updated, drastically reducing the attack surface.
Operational efficiency
Manual password management is not only time-consuming but also prone to errors. Automating this process with XOAP Windows LAPS DSC frees up IT resources and ensures that password policies are consistently applied across all machines.
Compliance and auditing
Regulatory frameworks often require strict password management practices. XOAP Windows LAPS DSC helps organizations meet these requirements by providing detailed logs and reports on password policy enforcement and changes.
Simplified management
With DSC, administrators can define the desired state of their infrastructure using configuration files. XOAP Windows LAPS DSC extends this capability to local administrator passwords, allowing for easy deployment and management through familiar DSC tools.
Getting started with XOAP Windows LAPS DSC
Prerequisites
Windows PowerShell: Make sure you have Windows PowerShell 5.1 or later installed.
DSC: Familiarity with the Desired State Configuration is beneficial.
Active Directory:
- Active Directory environment to manage domain-joined machines
- Update AD schema
- Grant permissions
- Check Domain Functional Level (DFL) prerequisites
- 📃 Get started with Windows LAPS and Windows Server Active Directory
- Entra ID (Azure AD ) environment to manage -joined machines
- Enable Local Administrator Password Solution (LAPS) setting
- 📃 Windows Local Administrator Password Solution in Microsoft Entra ID
Installation
To install the XOAP Windows LAPS DSC module, you can navigate to our Github repo. As with all other DSC modules that we provide, this one is free to use in and outside of the XOAP universe.
Download the files in the releases section and extract the contents into one of your locations that are used for searching modules. The list of locations can be shown by checking the value of the “$env:PSModulePath” variable.
An example of the standard path is: $Env:programfiles/WindowsPowerShell/Modules.
When you’re extracting the files, please use the correct folder structure:
XOAPWindowsLAPSDSC
|__0.0.2
|__DSCResources
| |__AzureADWindowsLAPSSettings
| |__LocalADWindowsLAPSSettings
| |__WindowsLAPSEmulationMode
|__Examples
|__Test
|__XOAPWinowsLAPSDSC.psd1
Configuration
For easier understanding how to use XOAPWinowsLAPSDSC module, below is documentation of used resources:
⭢ AzureADWindowsLAPSSettings
AzureADWindowsLAPSSettings [String] #ResourceName
{
[DependsOn = [String[]]]
[PsDscRunAsCredential = [PSCredential]]
[AdministratorAccountName = [String]]
[PasswordAgeDays = [Int32]]
[PasswordLength = [Int32]]
[PasswordComplexity = [Int32]]
[PostAuthenticationResetDelay = [Int32]]
[PostAuthenticationActions = [Int32]]
}
⭢ LocalADWindowsLAPSSettings
LocalADWindowsLAPSSettings [String] #ResourceName
{
[DependsOn = [String[]]]
[PsDscRunAsCredential = [PSCredential]]
[AdministratorAccountName = [String]]
[PasswordAgeDays = [Int32]]
[PasswordLength = [Int32]]
[PasswordComplexity = [Int32]]
[PasswordExpirationProtectionEnabled = [Boolean]]
[ADPasswordEncryptionEnabled = [Boolean]]
[ADPasswordEncryptionPrincipal = [String]]
[ADEncryptedPasswordHistorySize = [Int32]]
[ADBackupDSRMPassword = [Boolean]]
[PostAuthenticationResetDelay = [Int32]]
[PostAuthenticationActions = [Int32]]
}
⭢ WindowsLAPSEmulationMode
WindowsLAPSEmulationMode [String] #ResourceName
{
[DependsOn = [String[]]]
[PsDscRunAsCredential = [PSCredential]]
[AdministratorAccountName = [String]]
[PasswordAgeDays = [Int32]]
[PasswordLength = [Int32]]
[PasswordComplexity = [Int32]]
[PasswordExpirationProtectionEnabled = [Boolean]]
[AdministratorPasswordEnabled = [Boolean]]
}
Example
This is an example of a configuration that uses AzureADWindowsLAPSSettings:
configuration 'TestConfigAzureAD_
{
Import-DscResource -ModuleName 'XOAPWindowsLAPSDSC' -ModuleVersion '0.0.2'
AzureADWindowsLAPSSettings 'TEST'
{
AdministratorAccountName = 'TestAdmin'
PasswordAgeDays = '14'
PasswordLength = '16'
PasswordComplexity = '4'
PostAuthenticationResetDelay = '2'
PostAuthenticationActions = '1'
}
}
TestConfigAzureAD
Instead of writing this configuration in a code editor locally, you can also use XOAP. Using our DSC configuration wizard, you can create a LAPS configuration by using our simple-to-use frontend, create different versions of the configuration every time you save a change and prepare everything to deploy LAPS to multiple customers and groups.
⚙️ To create a new LAPS config you need to follow a few steps:
1. Navigate to the Configuration Management area, go to Configurations and click the + button to create a new configuration.
2. Define general settings like Name, Description and Tags and click “Add Resources”.
3. Select the “XOAPWindowsLAPSDSC” module, Version and Resource and configure the settings.
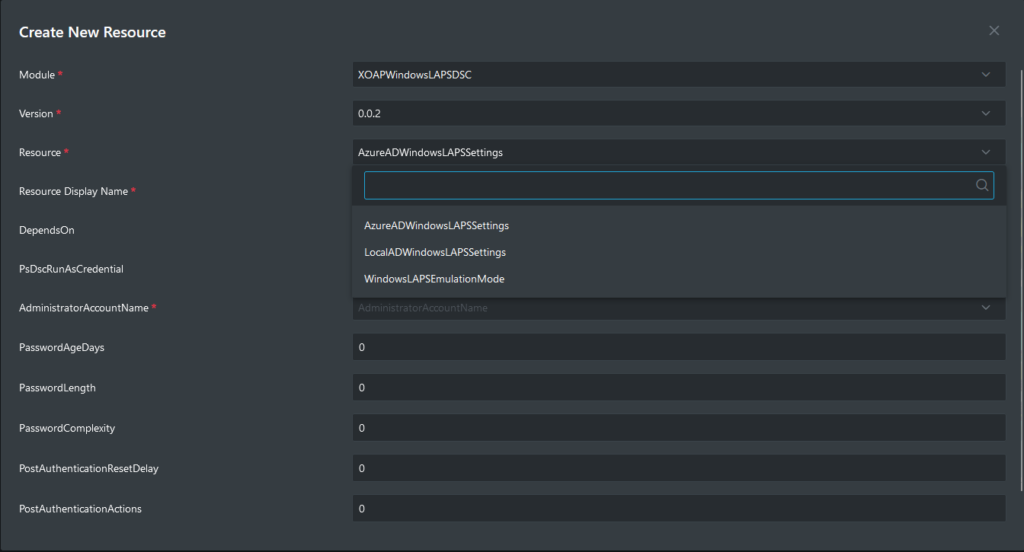
4. Once when all resources are configured, you can save the configuration and use it in Configuration Management groups to apply the settings to your nodes.
The good thing is, you don’t need to think about DSC syntax when you use XOAP to deploy LAPS configurations. The configuration wizard will guide you and it will allow you to input only valid types for parameters. Also, versioning of configurations allows you to easily change and deploy possible future changes of your LAPS configurations.
If you need more information about the Configuration Wizard, or how to apply configurations to your environments, please check our documentation. 📃
Your next step
In a time where cybersecurity threats are ever-evolving, taking proactive steps to secure your Windows environment is crucial. XOAP Windows LAPS DSC offers a comprehensive solution for automating local administrator password management, enhancing security and ensuring compliance.
By integrating this module into your infrastructure, you can streamline password management processes, reduce risks and focus on other critical aspects of your IT operations.
Explore more about XOAP Windows LAPS DSC on its GitHub repository and take the first step towards a more secure Windows environment! 🛡️